Fix SickBeard “Pushbullet Notification Failed” Error
 Getting the “Pushbullet Notification Failed” error from your SickBeard notifications? Well, the fix is simple, and here is what you have to do:
Getting the “Pushbullet Notification Failed” error from your SickBeard notifications? Well, the fix is simple, and here is what you have to do:
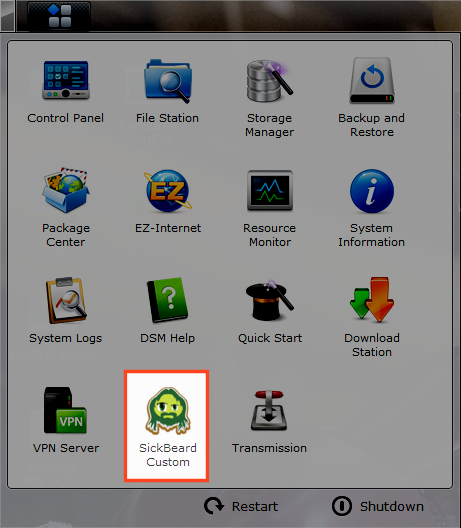
1) Find pushbullet.py in your SickBeard install directory. For me, this file was located in:
/volume1/@appstore/sickbeard-custom/var/SickBeard/sickbeard/notifiers
2) Open that file in your editor of choice, for me that is vi, and make the following change:
Find:
if method == ‘POST’:
uri = ‘/api/pushes’
else:
uri = ‘/api/devices’
And change to:
if method == ‘POST’:
uri = ‘/v2/pushes’
else:
uri = ‘/api/devices’
Note that the devices uri doesn’t change, you just need to update the pushes uri. I could dig in to the in’s and out’s of the Pushbullet API if I really felt like figuring out why this changed, but I don’t really care that much. I just wanted to get my notifications working again.
3) Write and Quit the changes and then restart SickBeard. This will recompile your changes in the python code and then hop in to your notifications and send a test message to make sure that worked.
That fixed it for me! Happy Pushbulleting 🙂
UPDATE 9/14/2014: Well, Something broke again. I couldn’t figure out what (I think it has to do with the JSON body but I didn’t feel like rewriting something that’s been fixed elsewhere), so I snagged the latest pushbullet.py from the troubled SickRage project and used that instead. Note, I had to switch the devices uri back to the /api/devices value because the /v2/devices value doesn’t work for me for some reason. Hopefully this doesn’t break again :-\
 I have been working on getting
I have been working on getting